Join Transform 2021 this July 12-16. Register for the AI occasion of the year.
A hybrid multicloud method can capitalize on legacy systems’ useful information and insights although applying the most current cloud-based platforms, apps, and tools. But finding hybrid multicloud safety appropriate is not effortless.
Exposing extreme safety weaknesses in hybrid cloud, authentication, and least privileged access configurations, the higher-profile SolarWinds breach laid bare just how vulnerable every single organization is. Clearly, enterprise leaders ought to see beyond the a great deal-hyped baseline levels of identity and access management (IAM) and privileged access management (PAM) now supplied by cloud providers.
In short, sophisticated persistent threat (APT) actors penetrated the SolarWinds Orion computer software provide chain undetected, modified dynamically linked library (.dll) files, and propagated malware across SolarWinds’ client base although taking unique care to mimic reputable visitors.
The terrible actors methodically studied how persistence mechanisms worked in the course of intrusions and discovered which procedures could avert detection as they moved laterally across cloud and on-premises systems. They also discovered how to compromise SAML signing certificates although applying the escalated Active Directory privileges they had gained access to. The SolarWinds hack shows what takes place when terrible actors focus on locating unprotected threat surfaces and exploiting them for information applying stolen privileged access credentials.
The incursion is especially notable for the reason that SolarWinds Orion is made use of for managing and monitoring on-premises and hosted infrastructures in hybrid cloud configurations. That is what tends to make eradicating the SolarWinds code and malware problematic, as it has infected 18 unique Orion platform solutions.
Cloud providers do their element — to a point
The SolarWinds hack occurred in an sector that relies significantly on cloud providers for safety handle.
A current survey by CISO Magazine discovered 76.36% of safety experts think their cloud service providers are accountable for securing their cloud situations. The State of Cloud Security Concerns, Challenges, and Incidents Study from the Cloud Security Alliance discovered that use of cloud providers’ more safety controls jumped from 58% in 2019 to 71% in 2021, and 74% of respondents are relying exclusively on cloud providers’ native safety controls today.
Image Credit: Cloud Security Alliance
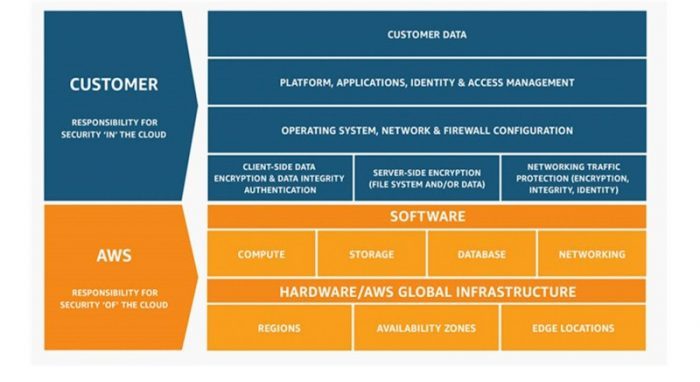
Taking the SolarWinds lessons into account, every single organization requirements to confirm the extent of the coverage offered as baseline functionality for IAM and PAM by cloud vendors. While the idea of a shared duty model is helpful, it is very important to look beyond cloud platform providers’ promises based on the framework.
Amazon’s interpretation of its shared duty model is a prime instance. It’s clear the company’s method to IAM, although centralizing identity roles, policies, and configuration guidelines, does not go far adequate to provide a completely safe, scalable, zero trust-based method.
The Amazon Shared Responsibility Model tends to make it clear the enterprise requires care of AWS infrastructure, hardware, computer software, and facilities, although prospects are accountable for securing their client-side information, server-side encryption, and network visitors protection — like encryption, operating systems, platforms, and client information.
Like competitors Microsoft Azure and Google Cloud, AWS offers a baseline level of assistance for IAM optimized for just its environments. Any organization operating a multi-hybrid cloud and constructing out a hybrid IT architecture will have wide, unsecured gaps among cloud platforms for the reason that each and every platform provider only presents IAM and PAM for their personal platforms.
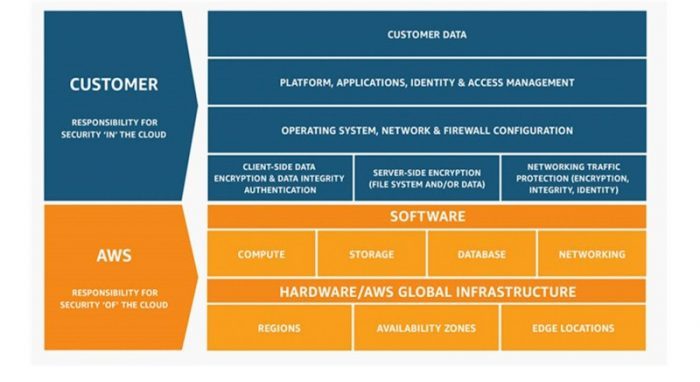
Image Credit: Amazon Web Services
While a helpful framework, the Shared Responsibility Model does not come close to giving the safety hybrid cloud configurations will need. It is also deficient in addressing machine-to-machine authentication and safety, an location seeing fast development in organizations’ hybrid IT plans today. Organizations are also on their personal when it comes to how they safe endpoints across all the public, private, and neighborhood cloud platforms they rely on.
There is at the moment no unified method to solving these complicated challenges, and every single CIO and safety group ought to figure it out on their personal.
But there requirements to be a single, unified safety model that scales across on-premises, public, private, and neighborhood clouds without having sacrificing safety, speed, and scale. Averting the spread of a SolarWinds-level attack begins with a single safety model across all on-premises and cloud-based systems, with IAM and PAM at the platform level.
Amid hybrid cloud and tool sprawl, safety suffers
The SolarWinds attack came just as multicloud solutions had began to achieve traction. Cloud sprawl is defined as the unplanned and normally uncontrolled development of cloud situations across public, private, and neighborhood cloud platforms. The top trigger of cloud sprawl is a lack of handle, governance, and visibility into how cloud computing situations and sources are acquired and made use of. Still, according to Flexera’s 2021 State of the Cloud Report, 92% of enterprises have a multicloud strategy and 82% have a hybrid cloud method.
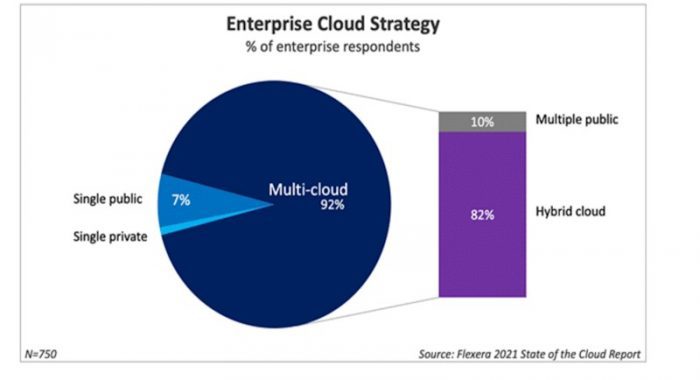
Image Credit: Flexera
Cloud sprawl takes place when an organization lacks visibility into or handle more than its cloud computing sources. Organizations are lowering the possible of cloud sprawl by obtaining a nicely-defined, adaptive, and nicely-understood governance framework defining how cloud sources will be acquired and made use of. Without this, IT faces the challenge of maintaining cloud sprawl in verify although attaining organization targets.
Overbuying safety tools and overloading endpoints with numerous, normally conflicting computer software customers weakens any network. Buying more tools could basically make a SolarWinds-level attack worse. Security teams will need to contemplate how tool and endpoint agent sprawl is weakening their networks. According to IBM’s Cyber Resilient Organization Report, enterprises deploy an typical of 45 cybersecurity-connected tools on their networks today. The IBM study also discovered enterprises that deploy more than 50 tools ranked themselves 8% reduced in their capability to detect threats and 7% reduced in their defensive capabilities than organizations employing fewer toolsets.
Rebuilding on a zero trust foundation
The SolarWinds breach is especially damaging from a PAM point of view. An integral element of the breach was compromising SAML signing certificates the terrible actors gained by applying their escalated Active Directory privileges. It was all undetectable to SolarWinds Orion, the hybrid cloud-monitoring platform hundreds of organizations use today. Apparently, a mixture of hybrid cloud safety gaps, lack of authentication on SolarWinds accounts, and lack of least privileged access made the breach undetectable for months, according to a Cybersecurity & Infrastructure Security Agency (CISA) alert. One of the most useful lessons discovered from the breach is the will need to enforce least privileged access across every single user and administrator account, endpoint, technique access account, and cloud administrator account.
The bottom line is that the SolarWinds breach serves as a reminder to strategy for and commence implementing zero trust frameworks that allow any organization to take a “never trust, always verify, enforce least privilege” method when it comes to their hybrid and multicloud approaches.
Giving customers just adequate privileges and sources to get their work accomplished and giving least privileged access for a particular time is necessary. Getting micro-segmentation appropriate across IT infrastructures will eradicate terrible actors’ capability to move laterally all through a network. And logging and monitoring all activity on a network across all cloud platforms is essential.
Every public cloud platform provider has tools accessible for undertaking this. On AWS, for instance, there’s AWS CloudTrail and Amazon CloudWatch, which monitors all API activity. Vaulting root accounts and applying multi-issue authentication across all accounts is a offered.
Organizations will need to move beyond the notion that the baseline levels of IAM and PAM delivered by cloud providers are adequate. Then these organizations will need to assume about how they can use safety to accelerate their organization targets by giving the customers they serve with least privileged access.
Adopting a zero trust mindset and framework is a offered today, as every single endpoint, technique access point, administrative login, and cloud administrator console is at danger if absolutely nothing alterations.
The lengthy-held assumptions of interdomain trust had been established incorrect with SolarWinds. Now it is time for a new, more intensely focused era of safety that centers on enforcing least privilege and zero-trust solutions across an complete organization.





/cdn.vox-cdn.com/uploads/chorus_asset/file/25547838/YAKZA_3840_2160_A_Elogo.jpg)
